Next NCM expansion - The Road to Governance Automated
For the last few months, I’ve been heads-down on the LARGncm (Network Configuration Management) platform. The goal wasn't just maintenance; it was to widen our scope and modernize the stack to prepare for the next major phase: Automated Governance.
Here is a look at the recent ecosystem expansion, a tech stack overhaul, and a necessary detour to build a rapid-response security tool.
1. Expanding the NCM Ecosystem
The first step was eliminating blind spots. I have added full support for two critical device families:
Aruba OS
Cisco FTD (Firepower Threat Defense)
This isn't just basic config backup. I built out the automation for Security Hardening Guides for both platforms immediately. I also took the opportunity to refactor the security report code across the entire application. The result is a faster, more unified reporting engine that treats new and legacy devices with the same level of scrutiny.
The Stack Upgrade I migrated the core platform to Django 6. Since this was just released, I expected some friction, but the transition was painless except for one minor aesthetic hiccup. We are now running on the absolute latest framework version, ensuring long-term stability and performance.
Visual Polish I also took the time to improve the general aesthetics and retired the old text-based daily reports. The new Daily Email is now a proper, beautifully formatted HTML report that makes digesting the morning status checks much easier.
2. A Necessary Detour: Project LARGshun
In the middle of this roadmap, reality intervened. We started getting hit by aggressive remote VPN brute-force attacks. The volume was high enough that it wasn't just a security annoyance; it was tripping Active Directory lockout thresholds, locking legitimate staff out of their accounts.
The Quick Fix (and its downside) We leveraged a recent feature in Firepower that allows us to block brute-forcing on remote access VPNs. We set the limit to 50 attempts—a limit high enough that we thought it would eliminate the risk of blocking real users. It worked instantly: the attacks were shunned, and the account lockouts stopped.
Eventually, however, a legitimate user tripped the threshold and got blocked. We realized we had no democratized way to "unshun" (unblock) them without manual engineering intervention.
The Solution: LARGshun I paused NCM dev for two days to code LARGshun. This is a dedicated Web UI that manages "shunned" IP addresses across our Cisco ASA, FTD, IOS, and Juniper devices.
Self-Service: Authorized users can view blocked IPs and "unshun" them instantly.
Audit Trail: Includes User Authentication, Role-Based Access Control (Admin vs. Standard), and session activity logging with email summaries.
The LARGshun Stack I wanted something lightweight and fast to deploy, so I stepped outside the main Django ecosystem for this tool:
Backend: Flask
State: Redis
Network Layer: Netmiko (for SSH)
Frontend: Tailwind CSS
Dev Note: This was my first time using Tailwind CSS, and it was excellent. The speed of styling and the quality of the out-of-the-box UI made the 2-day timeline possible.
3. NCM Next: Beyond the Network
As an ISP, our critical infrastructure is obviously network gear. However, we also rely on isolated Linux servers like our Speedtest servers that have historically been blind spots for NCM.
No more.
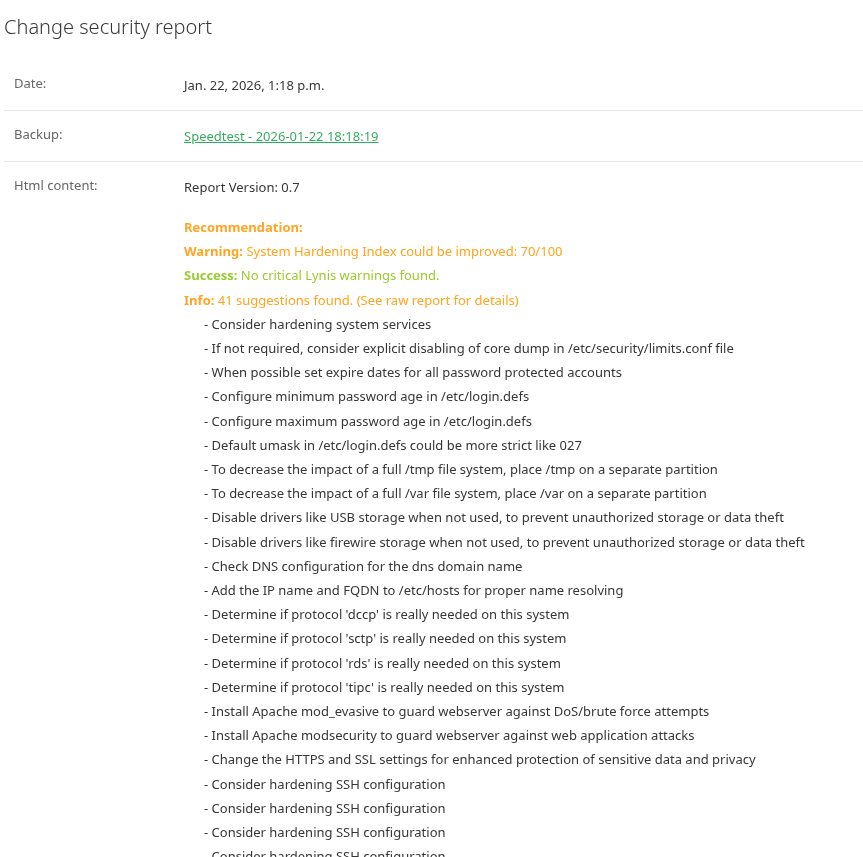
Although it’s not yet in production, I have Ubuntu Server and AlmaLinux (RHEL) running security reports in the development environment. The results are promising. While some of the hardening recommendations are a bit overkill for our specific use case, having that visibility is incredibly useful. If we have the time to harden them, why not?
The Microsoft Roadmap I plan to implement Pywinrm next to bring similar visibility to our Microsoft servers.
The End Goal Once the server integration is complete, we will practically be able to automate NIST 800-53 reports. Everything that matters, routers, switches, firewalls, Linux, and Windows, will be covered under a single governance umbrella.
Infact, other compliance reports are likely able to be automated as well.